1. Introduction: the day the patch answer fails
There’s a moment every experienced security team eventually faces.
A zero-day is disclosed. The exploit is real. The system is exposed. And then someone asks the question that sounds routine—but isn’t:
“When can we patch?”
You pause. Because this time, patching isn’t possible.
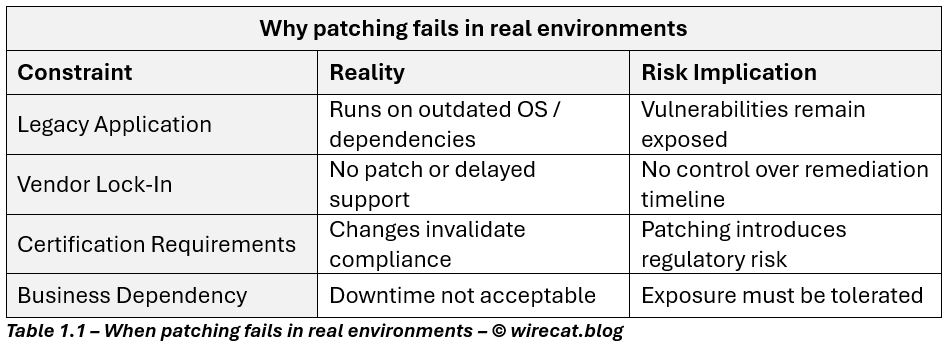
- The application is legacy but revenue-critical
- The vendor is slow, unresponsive, or contractually locked
- Upgrades would invalidate certification, break integrations, or introduce unacceptable downtime
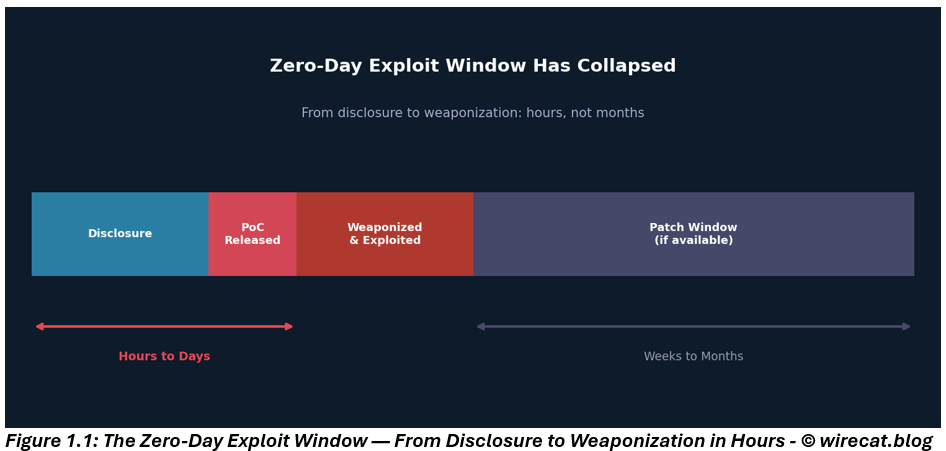
This scenario is no longer rare. In today’s threat landscape, where public proof-of-concepts are weaponized within hours and exploit techniques are rapidly commoditized, the window between disclosure and exploitation has effectively collapsed.
Yet the system remains in production. Business cannot stop. And the risk is already active.
This is where cybersecurity stops being theoretical and becomes risk management under constraint.
2. Why zero-day risk in legacy systems is fundamentally different
In modern environments, vulnerability management follows a familiar rhythm:
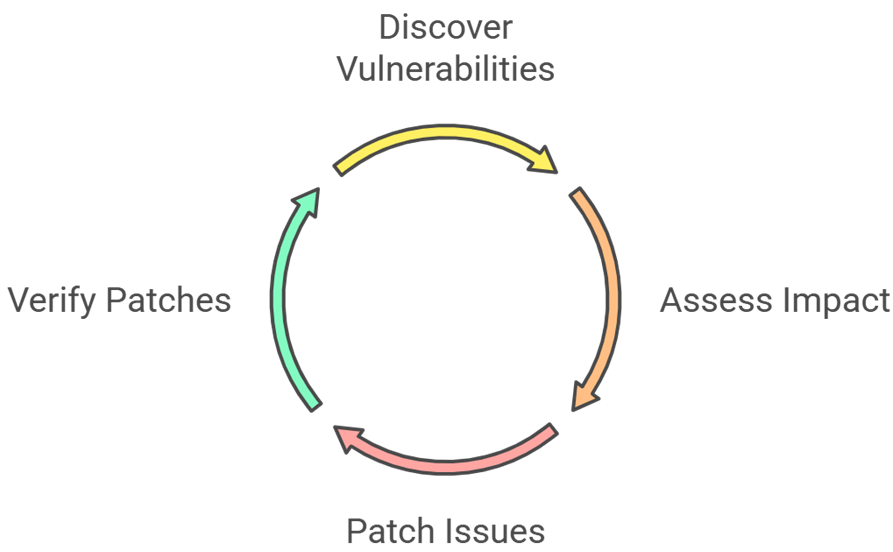
Legacy and vendor-locked systems break that cycle.
Here, zero-day risk isn’t just a vulnerability problem, it is a structural risk condition created by long-term technical debt, operational dependency, and external constraints.
Recent trends have made this even more challenging:
- Exploit commoditization and rapid weaponization
- Fileless and living-off-the-land attacks bypassing traditional defenses
- Delayed or unavailable vendor patches
At a risk level, four factors converge:
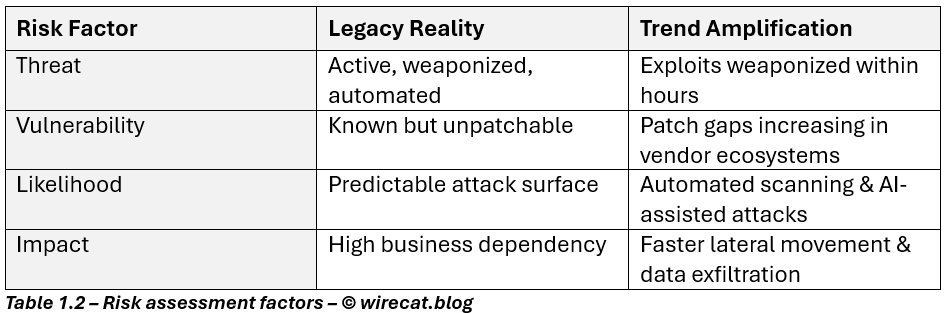
When one of the core risk treatments, patching, is unavailable, risk does not pause. It accumulates.
So the real question becomes: How do we reduce exploitability and impact when the vulnerability itself cannot be removed?
3. Reframing the problem: from vulnerability removal to exposure reduction
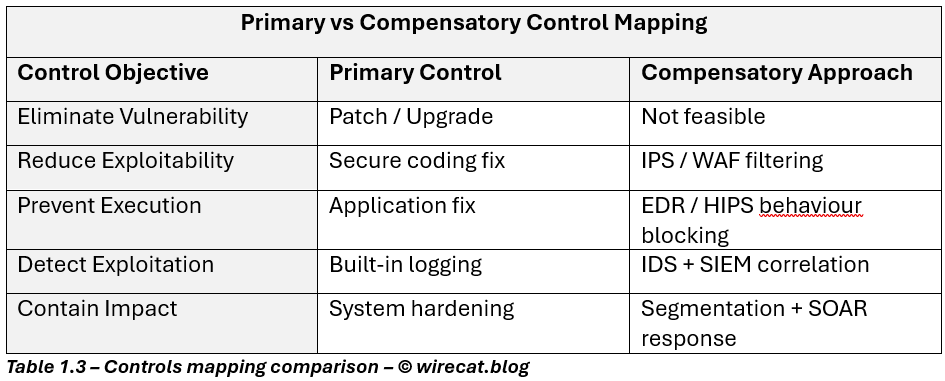
This is where mature security teams diverge from checkbox security. When the primary security control, timely patching, is unavailable, risk management does not stop. Instead, organizations invoke compensatory controls that provide equivalent or partial risk reduction until the primary control can be restored or the system retired.
As a result, risk treatment must shift focus:
- Away from eliminating vulnerability
- Toward reducing exposure, likelihood, and blast radius
In practical terms, we stop asking: “How do we fix the code?”
And start asking: “How do we break the attack path?”
4. Virtual patching — what it really is (and why it works)
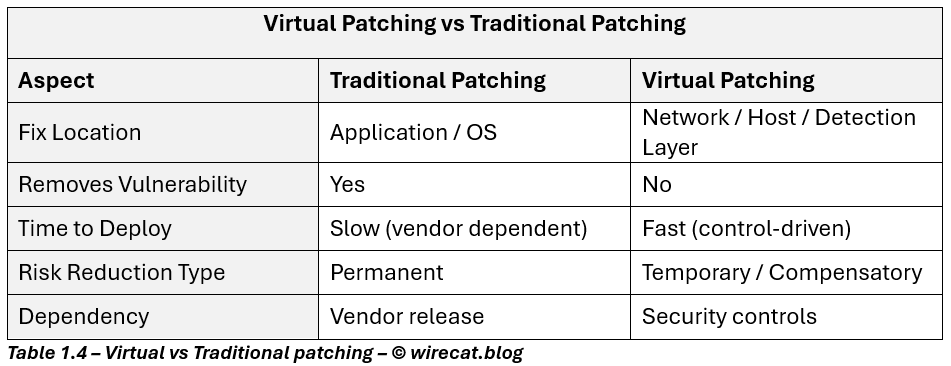
Virtual patching is often oversimplified as “IPS signatures” or “WAF rules.”
In practice, it is a risk control strategy, not a single control.
At its core, virtual patching means intercepting, detecting, or neutralizing exploit behaviour before it reaches the vulnerable component.
The vulnerability remains. The exploit path does not.
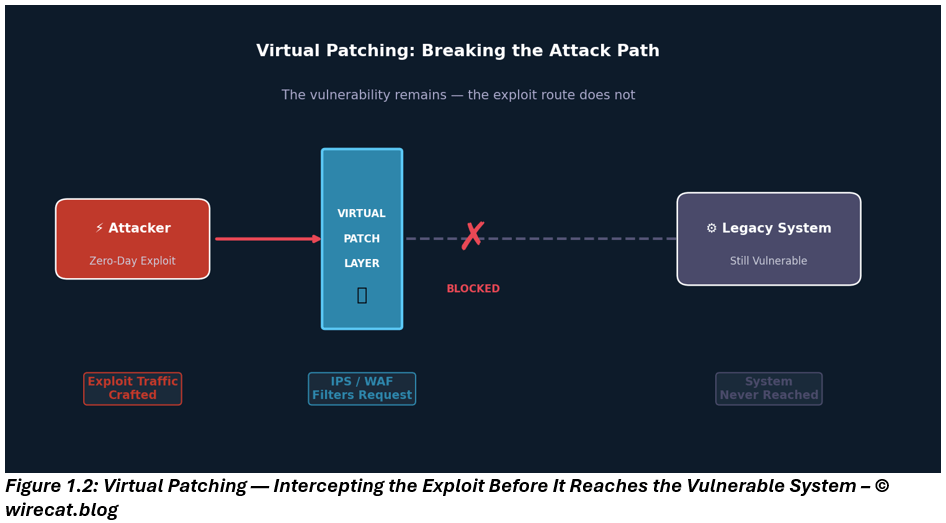
Virtual patching should be understood as a formally justified compensatory control and implemented when the primary control (patching) is infeasible due to operational, technical, or contractual constraints.
It compensates for the absence of the primary control by:
- Reducing exploitability
- Disrupting attack execution
- Enabling rapid detection and containment
5. The layered control model behind effective virtual patching
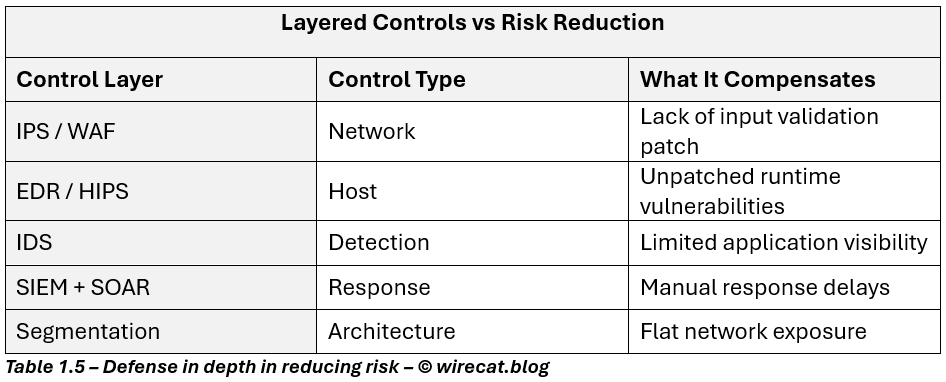
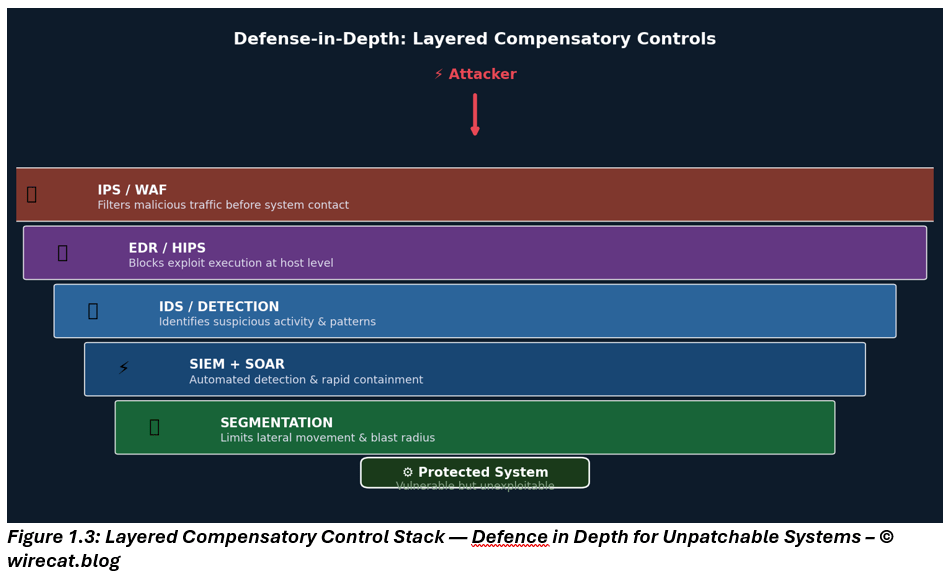
This layered approach is a practical application of defense in depth, where multiple compensatory controls collectively reduce risk when the primary control is unavailable.
In legacy and vendor-locked environments, virtual patching only becomes credible when implemented as a layered control stack.
No single control is sufficient. Risk reduction is achieved by stacking compensatory controls, each targeting a different dimension of risk.
Traffic-level enforcement (IPS, WAF): Reduces exploit success by filtering malicious traffic before it reaches the system.
Host-based exploit prevention (EDR / HIPS): Prevents execution of exploit techniques at runtime, including fileless attacks.
Detection & response (IDS + SIEM + SOAR): Identifies suspicious activity and enables rapid containment, reducing dwell time.
Segmentation: Limits lateral movement and reduces blast radius.
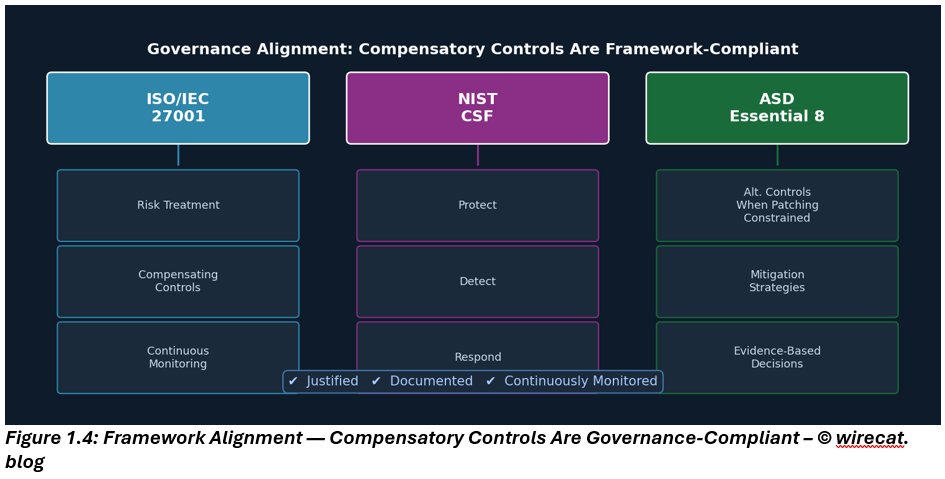
6. Governance alignment: why this stands up in audits and risk committees
This approach aligns naturally with risk-based security frameworks, even when primary controls are unavailable.
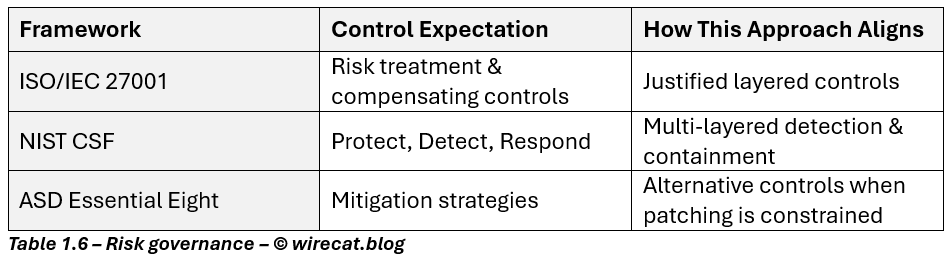
From a governance perspective, compensatory controls are acceptable when they are:
- Justified
- Documented
- Continuously monitored
None of these frameworks demand perfection. They demand defensible, risk-based decisions supported by evidence.
Closing thought
Legacy systems are not security failures. Ignoring their risk is.
In today’s threat landscape, where exploitation is faster, stealthier, and increasingly automated, waiting for a patch is not a strategy.
Virtual patching and exposure reduction are deliberate compensatory risk treatments, invoked when the primary control is unavailable and sustained until patching, system replacement, or decommissioning becomes possible.
In the next post, we will quantify how these controls reduce likelihood, dwell time, and impact, turning this approach into measurable, defensible risk management.
