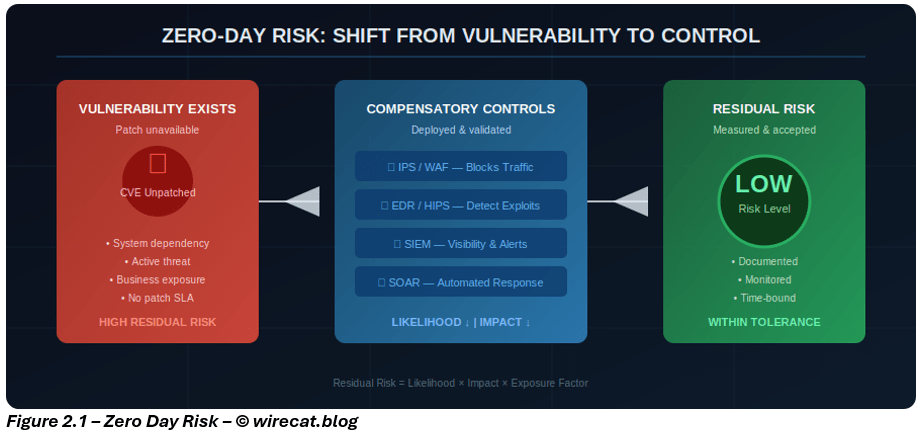
In Part 1, we established a hard truth: when patching is not possible, risk does not disappear, it just simply shifts.
The vulnerability remains. Business dependency remains. The threat remains. What changes is how disciplined your response becomes. This is where many organizations fall short.
They deploy compensatory controls, such an IPS signature here, a segmentation rule there, but struggle to answer the one question that matters most in an audit, risk committee, or executive review: “How do we know these controls are actually reducing risk?”
That question separates reactive security from mature risk management. Because in environments where patching is unavailable, confidence must come from evidence, not assumptions.
1. The problem with unmeasured compensatory controls
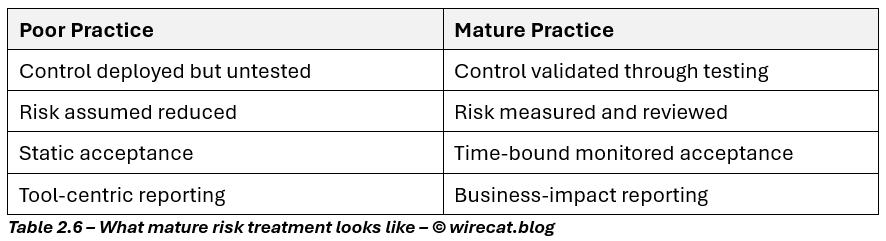
One of the most common mistakes in cyber risk management is treating compensatory controls as a comfort blanket rather than a measurable treatment.
Security teams often say:
- “We have IPS in place.”
- “EDR is monitoring.”
- “The system is segmented.”
But those statements alone do not prove risk reduction.
Why? Because the presence of a control is not the same as:
- effective coverage,
- operational tuning,
- rapid response capability, or
- sustained resilience.
In practice, poorly tuned compensatory controls can create a false sense of assurance. Especially in legacy environments where visibility is already limited.
That is why mature organizations do not just deploy controls. They measure how each control changes likelihood, exploitability, dwell time, and business impact.
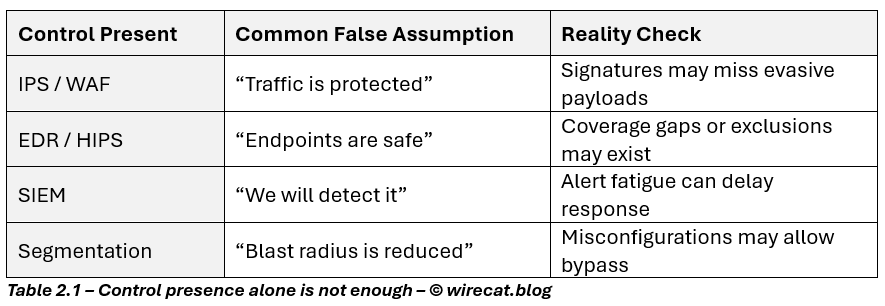
This is why evidence-based validation matters.
2. Start with risk in business terms, not technical terms
To quantify risk reduction properly, the first step is to stop thinking in terms of vulnerabilities alone. A zero-day in an unpatchable system is not simply a CVE. It is a business exposure scenario.
A mature assessment starts by asking:
- What business service does this system support?
- What happens if the system is unavailable for 4 hours? 24 hours?
- Could exploitation lead to data loss, safety impact, or operational disruption?
- What is the organization’s tolerance for downtime and loss?
This shifts the conversation from: “How severe is the vulnerability?” To: “How severe is the business consequence if the exploit succeeds?” That distinction is critical.
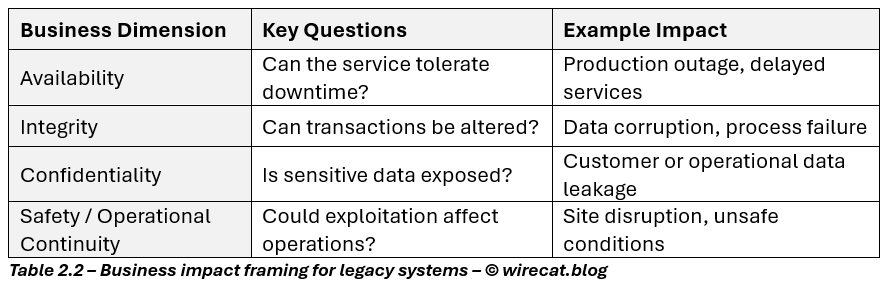
When the impact is clear, compensatory controls can be measured against real business outcomes.
3. The practical risk formula that matters
In real-world risk management, perfect precision is rarely possible. But structured estimation is far better than vague confidence.
When patching is not possible, organizations still need a practical way to determine whether compensatory controls are meaningfully reducing exposure. A simple residual risk model provides a structured way to make that judgment.
Residual Risk = Likelihood × Impact × Exposure Factor
Where:
- Likelihood = the probability of successful exploitation
- Impact = the business consequence if exploitation succeeds
- Exposure Factor = the degree to which the attack path remains open, based on control strength and operational visibility
To make this model usable, each variable should be scored against a defined scale. For example:
- Likelihood: 1 (rare) to 5 (almost certain)
- Impact: 1 (minor) to 5 (severe / critical)
- Exposure Factor: 0.2 (strong compensatory controls) to 1.0 (fully exposed)
This produces a numerical residual risk score, which can then be evaluated against the organization’s risk appetite, escalation criteria, and treatment thresholds.
The strength of this model lies in the fact that compensatory controls directly influence these variables. They may not remove vulnerability, but they can materially reduce the probability of exploit success, improve visibility, shorten response time, and limit operational impact.
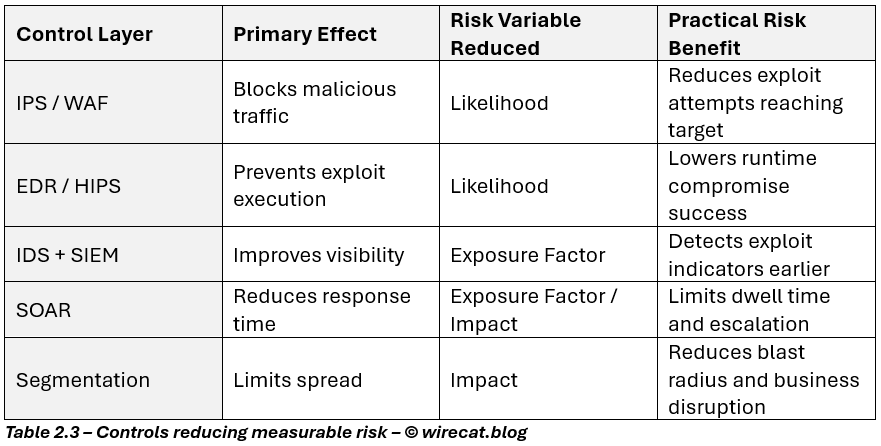
This is the essence of risk engineering: If you cannot remove the vulnerability, reduce the probability of successful exploitation and limit the consequences.
That is how organizations move from uncontrolled exposure to measurable, defensible residual risk.
4. Turning controls into measurable evidence
Compensatory controls only become credible when they are validated, tested, and regularly reviewed. In practice, organizations should assess four key dimensions to determine whether their controls are truly reducing zero-day risk.
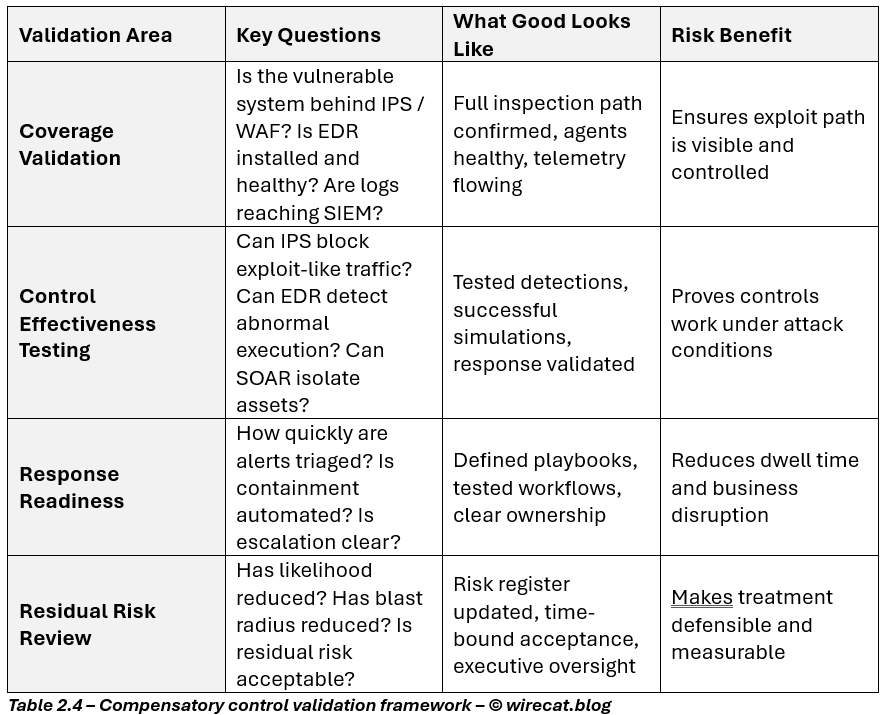
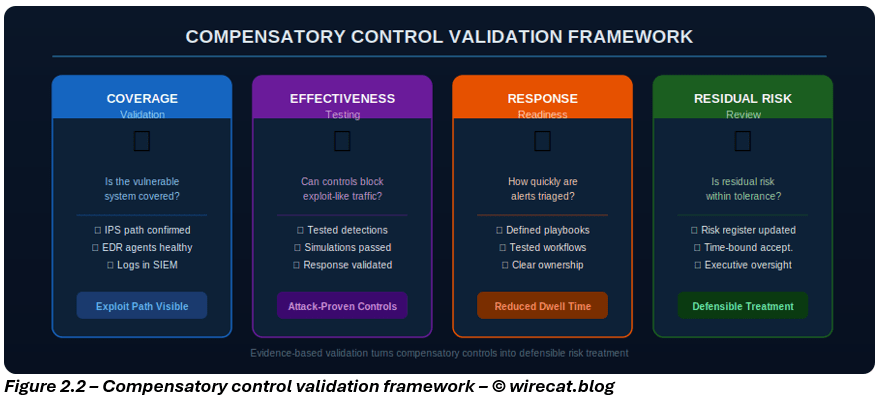
Validation on paper is not enough. To demonstrate that compensatory controls are working in practice, organizations need operational evidence that those controls are deployed, functioning as intended, and capable of responding under real attack conditions.
This evidence should be regularly reviewed and tied back to residual risk assessment.
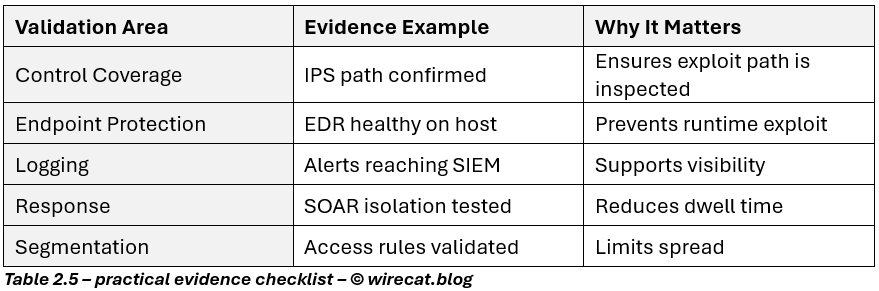
This is what turns compensatory control into a defensible risk treatment.
5. What good looks like in practice
A mature organization does not claim: “The risk is mitigated.”
It says: “The primary control is unavailable. Compensatory controls have reduced exploit likelihood, improved detection speed, and constrained business impact. Residual risk is documented, monitored, and within tolerance.”
That statement matters.
Because it is:
- technically honest,
- operationally realistic,
- governance aligned.
This is precisely how modern frameworks expect organizations to behave.
6. Why this matters now more than ever
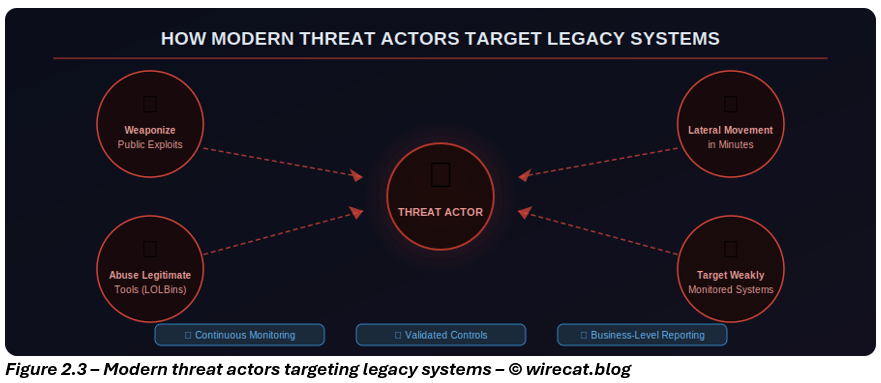
Modern attacks are faster, stealthier, and more adaptive than ever.
Today’s threat actors:
- weaponize public exploits quickly,
- abuse legitimate tools,
- pivot laterally in minutes,
- target weakly monitored legacy systems first.
That means organizations can no longer rely on:
- patch SLAs alone,
- annual reviews,
- or passive monitoring.
The future of cyber resilience is not just patching faster.
It is:
- measuring exposure continuously,
- validating compensatory controls regularly,
- and making risk visible in business terms.
Closing thought
Part 1 focused on a difficult reality: sometimes patching is not possible.
Part 2 is the discipline that follows: If you cannot eliminate vulnerability, you must prove that you have reduced the risk.
That is what separates a workaround from a mature risk treatment strategy.
In Part 3, we’ll take this one step further: How the same principles apply to OT, industrial systems, and critical infrastructure where patching delays are often the norm, not the exception.
